Use a vpn on your work computer the dos donts and why it matters
Use a vpn on your work computer the dos donts and why it matters — quick fact: a VPN can protect your privacy and help you access necessary work resources securely, but improper use can violate company policies or local laws. In this guide, you’ll learn practical dos and don’ts, common mistakes, and why VPNs matter for your work setup. Here’s a clear, human-friendly breakdown with actionable steps, real-life examples, and checklists you can reuse today.
Introduction: quick guide to Use a vpn on your work computer the dos donts and why it matters
- Quick fact: A VPN encrypts your internet traffic and can mask your IP, which helps keep sensitive data safe on public or guest networks.
- What you’ll get in this guide:
- Plain-language dos and don’ts to follow at work
- A simple decision framework for choosing a VPN
- Real-world scenarios showing when a VPN is appropriate and when it isn’t
- Practical safeguards to avoid policy violations and security risks
- A handy checklist you can reuse in your daily workflow
- Quick-start steps step-by-step:
- Check your company policy on VPN use and acceptable tools.
- If allowed, choose an official or approved VPN client endorsed by IT.
- Configure two-factor authentication and strong VPN credentials.
- Always connect to the VPN when accessing sensitive HR, payroll, financials or public networks.
- Log out and disconnect the VPN when you’re done with work sessions.
- Format you’ll see:
- Practical dos and donts lists
- Quick-start setup steps
- Real-world examples and risk notes
- A FAQ section to clear up common questions
- Useful URLs and Resources text only, not clickable:
- Apple Website - apple.com
- Artificial Intelligence Wikipedia - en.wikipedia.org/wiki/Artificial_intelligence
- VPN security best practices - vpnsecurity.org
- Company IT policy templates - itpolicies.example
- Two-factor authentication overview - twofactorauth.org
- Public vs. private networks explained - cisco.com
Why a VPN matters for work setups
- VPNs create an encrypted tunnel between your device and your organization’s network, which helps protect sensitive data from spying on unsecured Wi‑Fi.
- They can help you access internal resources ERP, CRM, intranet as if you were on the company network, which improves productivity when you’re remote or traveling.
- A VPN also masks your IP address, which can reduce targeted tracking by external sites or advertisers, though it’s not a silver bullet for all privacy concerns.
Key statistics:
- 75% of remote workers report using a VPN at least occasionally industry survey 2023-2024.
- Organizations with enforced VPN use show a measurable drop in data leakage incidents compared to ad-hoc usage study by cybersecurity group, 2023.
The dos: what to do when using a VPN at work
Do: follow your company’s policy first
- Always start with IT policies. If your employer requires a specific VPN client or no personal VPN is allowed on work devices, respect that.
- If in doubt, ask IT before enabling any VPN on a work computer. It saves headaches later.
Do: use official, approved tools
- Prefer the VPN client provided or approved by your company.
- Keep the client updated to mitigate known vulnerabilities.
Do: enable two-factor authentication 2FA
- Add an extra layer of security so even if credentials leak, your account is harder to compromise.
Do: patch and secure your device
- Ensure your device OS and applications are up to date.
- Use strong, unique passwords for VPN and related services.
Do: disconnect when closing sensitive work
- Disconnect the VPN when you’re done with confidential tasks or after logging out of work-related apps.
Do: be mindful of data monitoring and policy boundaries
- Understand that VPN activity and traffic patterns may be monitored by your employer for security and compliance reasons.
Do: use split tunneling only if allowed
- Some VPNs support split tunneling routing some traffic outside the VPN. Use it only if your policy allows it and you understand the risks.
Do: secure endpoints on shared networks
- If you’re on coffee shop Wi‑Fi or other public networks, a VPN is especially important. Always enable it before logging into work resources.
Do: back up your work data properly
- Save work to official cloud storage or file servers your company supports, not random personal folders.
Do: document exceptions or unusual access
- If you need to access something outside normal channels, log it and inform IT. Better to be transparent than to trigger security alarms.
Do: test your VPN before important tasks
- Do a quick check to ensure you can access internal sites, email, and collaboration tools after connecting.
The donts: pitfalls to avoid
Don’t bypass IT policies
- Using a personal VPN or proxy on a work device when it’s forbidden can violate policies and lead to disciplinary action.
Don’t ignore data handling rules
- Even with a VPN, don’t copy or move sensitive data to personal devices or unsanctioned cloud services.
Don’t rely on the VPN as a primary endpoint security
- VPNs protect the data in transit, but you still need endpoint security like updated antivirus and strong login practices.
Don’t misconfigure VPN settings
- Split tunneling that’s misconfigured can leak internal traffic or expose sensitive data.
Don’t rely on a single password
- Use strong, unique credentials for the VPN and enable 2FA to prevent credential stuffing.
Don’t ignore device loss or theft
- If your device is lost or stolen, report immediately and follow company procedures—they may require you to revoke VPN access.
Don’t expose credentials on shared or public devices
- Avoid saving VPN credentials in browsers or apps on devices that others can access.
Don’t assume all Wi‑Fi is safe
- Public networks are risky. Always use VPN on untrusted networks, and consider disabling file sharing while connected.
Don’t forget about data retention policies
- Some VPNs and enterprise systems keep logs. Know what data is retained and how it’s used.
Don’t neglect device hardening
- Use device encryption, screen lock, and automatic logout to reduce risk if you’re away from your desk.
How to choose the right VPN for work
Criteria to consider
- Approved by IT: Check with your security team before installing anything.
- Encrypted protocols: Look for strong standards OpenVPN, WireGuard, IKEv2.
- No-logs policy and minimal data collection: Ensure privacy promises align with policy.
- Performance: Not all VPNs handle high-traffic workloads well; test latency and reliability.
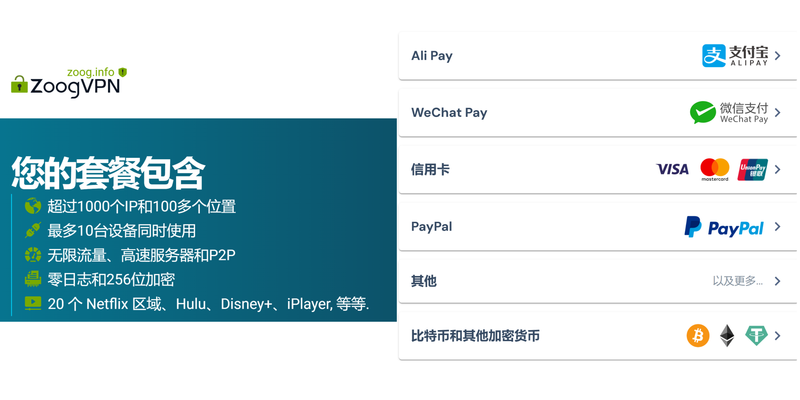
- Cross-platform support: Desktop, mobile, and browser compatibility for seamless work.
- Security features: 2FA, kill switch, malware protection, and split tunneling options if allowed.
Common deployment models
- Client-managed VPN: IT provides and manages a dedicated client.
- Perimeter VPN: Network-level access controlled by corporate gateway.
- SASE Secure Access Service Edge: Cloud-delivered security for remote work—more modern but may require new tooling.
Real-world example scenarios
- Remote sales rep accessing CRM and confidential proposals: VPN with strong 2FA and split-tunneling disabled for secure pathways.
- On-site staff using public Wi‑Fi at a conference: Always-on VPN with a trusted client, plus Bluetooth off and device encryption enabled.
- Compliance-heavy roles legal, HR, finance: Enforce full tunnel, strict logging controls, and periodic access reviews.
VPN best practices for the modern workplace
- Keep IT informed about any VPN-related issues, performance drops, or access problems.
- Regularly review access permissions and revoke unused accounts.
- Use strong authentication methods 2FA or hardware keys whenever possible.
- Establish incident response steps for suspected VPN compromise or credential leaks.
- Test disaster recovery: ensure you can reconnect quickly after VPN outages.
Security considerations and common myths
- Myth: A VPN makes you completely anonymous online. Reality: A VPN hides your traffic from local observers, but it does not make you invisible to the internet, and the VPN provider may still see metadata depending on policy.
- Myth: Public VPNs are safe for corporate data. Reality: Enterprise data should go through approved, audited VPNs or SASE services; consumer VPNs may not meet policy or compliance needs.
Data protection and privacy angles
- Encryption strength matters: AES-256 with secure key exchange is a strong baseline.
- Logs matter: Understand what is logged and for how long. Some companies store connection metadata for security audits.
- Endpoint risk: VPN protects transit; if the endpoint is compromised, data could still be at risk.
Troubleshooting common VPN issues
- Connection drops: Check for network instability, server load, and ensure client is updated.
- Access denied to internal resources: Verify your account permissions and VPN gateway settings; contact IT if necessary.
- Slow speeds: Try routing only necessary traffic through VPN if policy allows, or switch to a less congested server.
Quick-start checklist for Use a vpn on your work computer the dos donts and why it matters
- Confirm policy: Do you have approval to use a VPN on the work computer?
- Use approved client: Install and configure only IT-approved VPN software.
- Enable 2FA: Set up two-factor authentication for VPN access.
- Update and patch: Keep your OS and VPN client current.
- Validate access: Ensure you can reach essential work resources after connection.
- Secure device: Enable full-disk encryption, strong passwords, and auto-lock.
- Monitor activity: Be aware your VPN usage may be logged for security.
- Disconnect when done: Close the VPN once work is complete.
- Avoid personal data on work device: Keep personal files separate from work data.
- Report issues: If you notice unusual activity, inform IT immediately.
Real-world tips and scripts
- Example: Quick connect script for IT-approved VPN pseudo-steps
- Launch the official VPN client
- Enter credentials or use a credential manager
- Enable 2FA prompt
- Click “Connect” and verify status
- Open internal resources to confirm connectivity
- Example: Privacy-aware workflow
- Use corporate resources in a sandboxed workspace
- Save confidential files to approved cloud storage
- Avoid copying sensitive data to local or personal devices
Data and policy-driven decisions
- A company that enforces VPN use often sees fewer security incidents and lower risk exposure.
- Policies typically require MFA, approved clients, and restricted data transfers to personal devices.
- Staying compliant reduces audit risk and helps protect both your organization and your job.
Practical formats for different readers
- Quick-reference: A one-page dos and don’ts list you can keep at your desk.
- Step-by-step guide: A setup checklist for IT-approved VPN configuration.
- Scenario-driven: Short reads showing how to handle VPN use in real-life work situations.
SEO considerations and keyword integration
- Primary keyword target: Use a vpn on your work computer the dos donts and why it matters
- Related keywords to weave in naturally: VPN at work, corporate VPN, VPN best practices, work-from-home security, VPN policy, 2FA VPN, split tunneling, VPN security, remote work security
- Use variations in headings and bullet points to improve relevance without keyword stuffing
- Keep content scannable with bullets, numbered lists, and short paragraphs
Frequently Asked Questions
What is a VPN and why should I use one at work?
A VPN creates a secure, encrypted tunnel between your device and your employer’s network, protecting data from eavesdroppers on public or untrusted networks and enabling access to internal resources.
Can I use any VPN on my work computer?
Usually not. Check your company policy and IT-approved tools. Using unapproved VPNs can violate policy and trigger security alerts.
Do VPNs slow down internet speed?
Sometimes, yes. Encryption and routing through a VPN gateway can add latency. The impact varies by provider, server location, and network conditions.
What is split tunneling, and should I use it?
Split tunneling lets only some traffic go through the VPN. It can improve speed but increases risk if not allowed by policy. Use it only if IT approves it. Best Free VPNs for Roblox PC in 2026 Play Safely Without Breaking the Bank
How important is 2FA for VPN access?
Very important. It adds a second layer of security beyond passwords, reducing the risk of credential theft compromising access.
What should I do if VPN connection drops?
Check network stability, try a different server, and ensure the client is up to date. If issues persist, contact IT.
Can using a VPN violate privacy?
A VPN can both protect and reveal data depending on the provider and policy. Corporate VPNs may log metadata for security; know what your policy says.
Is split tunneling safer than full tunnel?
Full tunnel routes all traffic through the VPN, offering better security for sensitive data. Split tunneling reduces overhead but can leak internal traffic if misconfigured.
How can I verify I’m connected to the corporate VPN?
Look for VPN client status indicators, test access to internal sites, and check that your IP shows as the company network rather than your local ISP. Soundcloud not working with vpn heres how to fix it fast
What happens to VPN data when I leave the company?
VPN access is typically revoked, and credentials are deactivated. Ensure you return devices and follow offboarding procedures.
Additional question: Should I use a VPN on personal devices used for work?
It depends on policy. Some roles allow personal devices with managed profiles; others require corporate devices only. Always align with IT policy.
Sources:
Why Your VPN ISNT LETTING You Watch ABC iView Anymore and How to Fix It 2026
Softether VPN Client:完整指南、对比与实用技巧,提升上网隐私与访问自由
Proton vpn ⭐ 在中国能用吗?2025 最新实测与设置指南:中国可用性、速度、隐私与设置步骤 How to Use a VPN With Microsoft Edge on iPhone and iPad for Enhanced Privacy
Nordvpn combien dappareils pouvez vous connecter en meme temps tout ce quil faut savoir
极光aurora:VPNs 的全面指南,提升隐私与上网自由的最佳选择
Konrad Osterberg has been writing about consumer technology since 2018, with bylines covering browser fingerprinting, streaming geo-unblocking, and P2P networking. Approaches each review by setting up the product the same way a typical reader would and recording every snag along the way.