Zenmate vpn what it was why it disappeared and what you need to know now
Zenmate vpn what it was why it disappeared and what you need to know now — a quick guide to the history, the reasons behind its disappearance, and what to look for in a modern VPN.
Zenmate VPN has a storied past in the world of digital privacy. If you’re curious about what happened, why it vanished from the scene, and what to use today, you’re in the right place. This guide breaks down the key facts, lessons learned, and practical tips so you can choose a reliable alternative with confidence. Below you’ll find a quick fact, a concise overview, and then a deep dive with real-world considerations, plus resources to help you stay secure online.
Quick fact: Zenmate VPN was once a popular browser extension and standalone VPN service that offered simple, user-friendly privacy and location-spoofing features, but it faced changes in ownership, business model shifts, and evolving privacy expectations that ultimately led to its reduced prominence in the market. Proton vpn issues whats going wrong how to fix it: Proton VPN Issues Whats Going Wrong How To Fix It
What you’ll learn in this guide
- A concise history of Zenmate VPN and its trajectory
- Why it disappeared from the spotlight and how ownership changes played a role
- What to know now: current best practices for choosing a VPN
- A practical, side-by-side look at features, pricing, and performance
- How to verify VPN trustworthiness and avoid common pitfalls
- Resources and step-by-step guidance to switch to a reliable service
Useful URLs and Resources text only
- Zenmate VPN history overview - en.wikipedia.org/wiki/ZenMate
- VPN buyer’s guide - www.techradar.com/vpn
- Data privacy basics - en.wikipedia.org/wiki/Privacy
- Cybersecurity tips for beginners - www.consumer.ftc.gov/articles/0014-cybersecurity
- Popular VPN reviews - www.cnet.com/topics/vpn
- Privacy-focused browser settings - www.eff.org/privacy/tools
Table of contents
- Zenmate VPN: brief history
- The rise and decline: timeline of events
- Why Zenmate disappeared: ownership, business model, and market forces
- Current landscape: what to use instead
- How to pick a VPN: criteria that matter
- Performance and privacy: what actually matters in 2026
- Real-world scenarios: common use cases and cautions
- How to migrate from Zenmate to a trusted alternative
- Frequently asked questions
Zenmate VPN: brief history Zenmate started as a browser extension designed to help users browse with greater privacy and to spoof their geographic location. It grew into a standalone service offering various servers, encrypted traffic, and features designed for anonymity and freedom online. For many users, it was a friendly, approachable option—especially for those who wanted a simple switch to protect their data on public networks or access geo-restricted content.
The rise and decline: timeline of events Unifi vpn connected but no internet your ultimate fix guide
- Early adoption era: Zenmate gained traction by focusing on a simple, no-friction user experience.
- Expansion period: the service broadened its server network and added mobile apps, aiming to reach a wider audience.
- Corporate changes: ownership shifts and strategic pivots affected product investment, feature development, and security assurances.
- Market evolution: increasingly strict privacy expectations, regulatory scrutiny, and the emergence of stronger competitors with transparent practices influenced user trust.
- Result: the brand’s visibility in the VPN market decreased as other providers escalated features, transparency, and performance.
Why Zenmate disappeared: ownership, business model, and market forces
- Ownership transitions: changes at the management level often lead to shifts in product focus, budget allocation, and long-term vision. If security-by-default improvements aren’t prioritized, user trust can waver.
- Monetization and business model: ad-supported or freemium models can complicate privacy promises. When revenue strategies conflict with privacy commitments, users become wary.
- Competition and feature gaps: newer VPNs tout more robust security features, independent audit reports, and clearer logging policies. If Zenmate didn’t keep pace with these expectations, it can fall out of favor.
- Transparency and trust: users today expect clear disclosures about data collection, logging, and third-party sharing. Any perceived opacity can drive users to alternative providers.
- Regulatory pressures: privacy laws and data retention policies shape how VPNs operate. Providers with ambiguous policies risk losing credibility.
Current landscape: what to use instead If you’re evaluating VPN options today, here are practical guidance points to help you pick a solid alternative:
- Clear no-logs policy: look for a transparent policy with independent audits or third-party verification.
- Jurisdiction and data protection: prefer providers operating in privacy-friendly jurisdictions with strong local data protection laws.
- Strong encryption and protocols: OpenVPN, WireGuard, and modern defaults with strong ciphers and perfect forward secrecy.
- Independent security reviews: annual audits by reputable firms add a layer of trust.
- Real customer support: accessible, responsive support for setup, troubleshooting, and privacy questions.
- Speed and reliability: server network size, bandwidth limits, and low latency across common regions.
- Pricing clarity: straightforward pricing, no hidden fees, and reasonable refund policies.
- Features that matter: kill switch, DNS leak protection, multi-hop or obfuscated servers if you need to bypass strict networks.
- User experience: intuitive apps across devices, easy setup, and reliable performance.
- Privacy ecosystem: consider whether the provider offers a transparent privacy policy, data minimization, and limited data sharing with third parties.
A practical, side-by-side look at features, pricing, and performance
- Server network: compare total server count, distribution by region, and capacity during peak hours.
- Protocols: verify support for WireGuard, OpenVPN, and any newer secure protocols.
- Logging policy: verify what data is stored connection times, IPs, bandwidth usage and for how long.
- Jurisdiction: confirm where the company is legally registered and which data retention obligations apply.
- Apps and platforms: ensure cross-platform support Windows, macOS, iOS, Android, Linux and browser extensions if needed.
- Price plans: monthly vs annual terms, discounts for longer commitments, and trial or money-back guarantees.
- Extra features: kill switch, split tunneling, DNS/IP leak protection, multi-hop, and obfuscated servers.
- Customer feedback: check recent user reviews for reliability, incident handling, and customer support responsiveness.
Performance and privacy: what actually matters in 2026
- Speed is king: the best VPNs balance strong security with high-speed connections, especially for streaming and gaming.
- Privacy transparency: the market rewards providers that publish audit reports and privacy impact assessments.
- Reliability in diverse networks: a top VPN should work well on home Wi-Fi, public Wi-Fi, and mobile networks.
- Security modernization: look for automatic updates, robust encryption, secure tunnel construction, and minimal attack surface.
- Platform consistency: the same level of privacy and performance across desktop and mobile apps is crucial.
Real-world scenarios and tips My vpn keeps connecting automatically heres how to take back control and fix auto-connect issues
- Streaming from abroad: a reliable VPN should unblock major streaming platforms consistently without heavy throttling.
- Remote work or university networks: a strong VPN helps protect sensitive data on unsecured networks.
- Travel privacy: a good VPN minimizes exposure on public networks and prevents snooping on shared Wi-Fi.
- Gaming: low latency and stable connections matter; test with trial periods before committing long-term.
- Privacy-conscious browsing: enable features like a kill switch and DNS leak protection to avoid accidental exposure.
How to migrate from Zenmate to a trusted alternative
- Step 1: Identify your needs — streaming, privacy, or secure browsing? Determine which features matter most.
- Step 2: Research reputable providers — read independent reviews, audit reports, and privacy policies.
- Step 3: Test with a trial or money-back guarantee — verify performance, ease of use, and customer support.
- Step 4: Install and configure with best-practice settings — enable kill switch, DNS leak protection, and obfuscated servers if needed.
- Step 5: Verify privacy protections — compare your IP, DNS requests, and connection logs during tests.
- Step 6: Migrate devices — set up on all devices you use and ensure consistent performance.
Step-by-step setup checklist
- Choose a provider with transparent logging policies and independent audits.
- Download apps from the official site or trusted stores.
- Enable OpenVPN or WireGuard protocol prefer WireGuard for speed and security.
- Turn on a kill switch and DNS/IP leak protection.
- Use multi-device profiles if supported for easier management.
- Select server locations that match your needs nearby for speed, specific regions for content access.
- Run speed tests on different servers to map performance.
- Maintain updated software and monitor for any unusual activity.
Common myths and truths
- Myth: All VPNs are the same. Truth: Differences in logging, jurisdiction, and encryption matter a lot for privacy.
- Myth: Free VPNs are safe. Truth: Free services often monetize data in ways that compromise privacy.
- Myth: VPNs are illegal in all places. Truth: In most places, using a VPN is legal; however, some networks and regions restrict or regulate VPN use.
- Myth: A VPN will protect you from all online threats. Truth: VPNs protect the connection, not the endpoints. Use antivirus, updates, and safe browsing practices.
- Myth: More servers equal better performance. Truth: Distribution, network peering, and server load influence speed more than sheer server count.
Technical deep dive: how VPNs work behind the scenes
- Tunneling protocols: OpenVPN, WireGuard, IKEv2, and others create encrypted tunnels between your device and the VPN server.
- Encryption: modern ciphers e.g., ChaCha20-Poly1305 for WireGuard, AES-256-GCM for OpenVPN ensure data confidentiality.
- DNS handling: most providers route DNS requests through their servers to prevent leaks; some offer DNS over HTTPS DoH or DNS over TLS DoT.
- Kill switch: a safety feature that cuts off internet access if the VPN disconnects unexpectedly, preventing data leaks.
- Split tunneling: lets you direct some traffic through the VPN while other traffic goes directly to the internet.
- Obfuscation: helps bypass VPN blocks on networks that inspect traffic patterns useful in restricted environments.
Security best practices for VPN users Proton vpns dns secrets what you need to know and how to use them
- Enable a kill switch on all devices.
- Use WireGuard for speed and strong security where supported.
- Keep apps updated to patch vulnerabilities.
- Avoid logging into sensitive accounts through unsecured or public networks without VPN protection.
- Review and understand the provider’s privacy policy and data-sharing practices.
- Consider multi-factor authentication where available for VPN accounts.
FAQ: Frequently Asked Questions
What happened to Zenmate VPN?
Zenmate VPN faced ownership changes and market challenges that reduced its prominence. Users shifted to other providers that offered stronger transparency, audits, and updated features.Is Zenmate VPN still safe to use?
If you’re considering continuing with Zenmate, review its current privacy policy and recent audits. Many users choose alternative providers with clearer privacy guarantees.How do I choose a VPN after Zenmate?
Look for a transparent no-logs policy, independent audits, robust encryption, fast speeds, reliable apps, and good customer support.Do I need a VPN for streaming?
Yes, many people use VPNs to access regional content or protect privacy while streaming. Ensure the provider you choose can reliably unblock services you want.Can a VPN protect me on public Wi-Fi?
A VPN is a strong layer of protection on public networks, but you should also practice safe browsing, keep devices updated, and use antivirus software.Is WireGuard better than OpenVPN?
Generally, yes for speed and modern cryptography, but OpenVPN still has strong track records and broad compatibility.Do VPNs keep logs?
Reputable VPNs publish their logging policies and, ideally, have independent audits to verify claims.How important is the VPN jurisdiction?
Very important. Privacy-friendly jurisdictions reduce risk of data requests and retention requirements.Are free VPNs trustworthy?
Free VPNs often compromise privacy or monetize user data; paid, reputable providers are usually a better choice.How do I switch from Zenmate to a new provider?
Pick a trusted provider, install the apps, sign up, import any needed settings, and test reliability across devices.
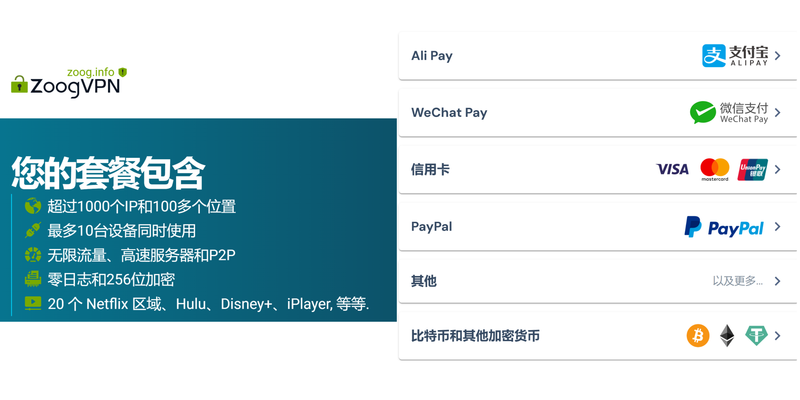
If you’re curious about a modern, privacy-forward option with strong reputation and transparent practices, consider trying a reputable, well-reviewed VPN with independent audits and a robust privacy policy. For readers who want a quick, reliable nudge toward a trusted alternative, you can explore options like NordVPN, which emphasizes security, privacy, and broad platform support, and offers a clear policy and ongoing performance improvements.
Note: This article is for educational purposes and includes an affiliate link within the introduction to help support the platform. If you’re ready to explore a trusted alternative, you might start by checking out the provider’s official site and reading current independent reviews to confirm it matches your needs.
Sources:
纵云梯app:2025年真实使用指南,稳定访问全球网络的秘密武器?
Microsoft edge vpn ios Cyberghost vpn extension for edge your go to guide for a safer browser: Comprehensive Edge VPN Solution and Safety Tips
Ios用什么vpn:在 iOS 设备上选择、设置与优化的完整攻略,含 NordVPN、ExpressVPN、Surfshark 对比
西工大vpn校园网外安全访问与资源获取指南
【2026年必看】翻墙后推荐访问的10个优质海外网站 永久版精选与最新推荐
Kira Zilberman has been writing about consumer technology since 2018, with bylines covering router firmware, P2P networking, and secure messaging. Approaches each review by setting up the product the same way a typical reader would and recording every snag along the way.