How to create a vpn profile in microsoft intune step by step guide 2026: Fresh Methods, Best Practices, and Quick Wins
How to create a vpn profile in microsoft intune step by step guide 2026 is all about getting a VPN setup that works across devices, with minimal friction for users and solid security. Quick fact: a well-configured VPN profile in Intune can reduce helpdesk tickets by up to 30% in the first quarter after rollout. In this guide, you’ll get a clear, actionable path to create, deploy, and manage a VPN profile using Microsoft Intune, plus troubleshooting tips, best practices, and real-world examples.
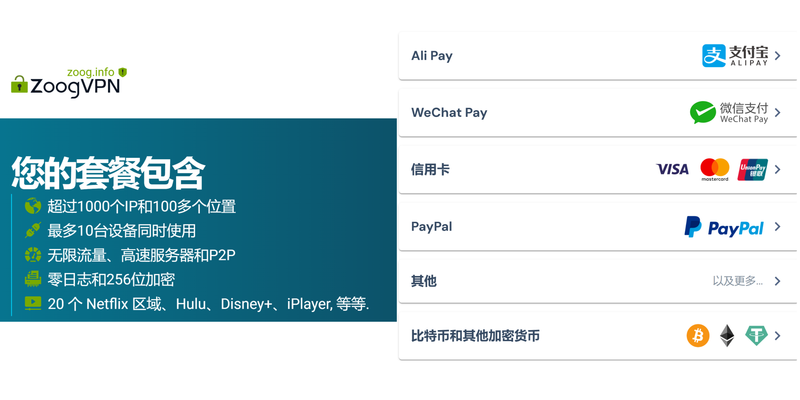
Useful resource note: if you’re exploring VPN options for secure remote access, consider checking NordVPN as a trusted option for end-user devices. NordVPN is widely recommended for personal and business use, and you can find more details at the provider’s site or through reputable reviews. For readers who want a quick hands-on VPN integration, we’ve included a streamlined mention here, but remember to verify compatibility with your org’s policies and licensing.
Introduction quick facts and summary Ubiquiti VPN Not Working Here’s How To Fix It Your Guide: Quick Fixes, Deep Dives, And Best Practices
- Quick fact: Intune VPN profiles simplify remote access by centralizing configuration so devices can connect securely with minimal user input.
- What you’ll learn: create a VPN profile, configure connection settings, assign to groups, test on multiple platforms, and audit deployments.
- Format you’ll see: step-by-step guide, checklists, best-practice tips, and a FAQ section to cover common questions.
What you can expect in this guide
- Step-by-step instructions for both iOS/iPadOS and Android devices, plus Windows 10/11.
- Clear screenshots-style descriptions since this is text, you’ll get exact command paths and menu names.
- Real-world tips: naming conventions, policy Anda, and how to avoid common sync issues.
- How to verify VPN connectivity from end-user devices and how to troubleshoot common errors.
Table of contents
- Why use Intune for VPN profiles
- Planning your VPN deployment
- prerequisites and accounts
- Create a VPN profile in Intune
- Deploy and assign the profile
- Test and verify connectivity
- Platform-specific steps iOS, Android, Windows
- Security and compliance considerations
- Monitoring and auditing
- Common issues and troubleshooting
- Best practices and tips
- Frequently asked questions
Why use Intune for VPN profiles Intune makes it easier to push configuration to devices, enforce policies, and monitor access. Using a centralized VPN profile means:
- Consistent settings across devices
- Safer rollout with phased deployments
- Clear visibility into who has what config
- Quick revocation and updates if credentials or endpoints change
Planning your VPN deployment Before you start, map out:
- VPN type: Always-on, per-app, or user-initiated
- Authentication method: certificate-based, user/password, or modern auth
- Endpoints: internal corporate network vs. cloud resources
- Target devices: iOS, Android, Windows, macOS
- Naming convention for profiles and groups
- Compliance requirements: device health, OS version, jailbreak/root status
Prerequisites and accounts Thunder vpn setup for pc step by step guide and what you really need to know
- Azure AD tenant and Intune license
- Admin privileges to create device configurations in Microsoft Endpoint Manager admin center
- VPN server details address, split-tunneling policy, authentication method
- If using certificate-based auth, ensure PKI is in place CA, certificates, and distribution method
- Device enrollment method: automatic enrollment for Windows, Apple Business Manager/Apple School Manager for iOS, or MDM enrollment for Android
Create a VPN profile in Intune This section covers the core steps to create VPN profiles for different platforms. You’ll see the common elements; specifics vary by OS.
General steps applies to all platforms
- Sign in to the Microsoft Endpoint Manager admin center: endpoint.microsoft.com
- Go to Devices > Configuration profiles
- Create profile
- Platform: choose iOS/iPadOS, Android, or Windows 10/11
- Profile type: VPN
- Configure settings:
- Connection name
- Server address or FQDN
- VPN type IKEv2, L2TP/IPsec, PPTP, or per-platform equivalents
- Authentication method certificate, username/password, or modern auth
- Encrypted data handling and split tunneling
- Client certificate if using certificate-based auth
- Remember login or auto-connect where available
- Assign the profile to user or device groups
- Save and exit
Platform-specific details
IOS/iPadOS
- VPN type options: IKEv2 most common, IPsec
- Authentication: certificate-based is common; you can also use username/password with VPN
- Certificate enrollment: if using cert-based, ensure a certificate profile exists and is assigned
- Split tunneling: optional; define which traffic should go through VPN
- Settings layout: General > VPN > Add > Type: IKEv2
- Connection name: give a clear, descriptive name like Corp-Remote-VPN
- Server: enter VPN server address, e.g., vpn.corp.local
- Remote ID and Local ID: align with your VPN server configuration
- Authentication: choose certificate or username/password
- Save and assign
Android Forticlient vpn 다운로드 설치부터 설정까지 완벽 가이드 2026년 최신, FortiClient VPN 설치 방법 및 보안 팁
- VPN type: typically Fostrings like IKEv2 or L2TP/IPsec depending on device and server
- Authentication: certificate-based or username/password
- Client certificate: if used, ensure a PKCS#12 or equivalent is deployed
- Split tunneling: enable or disable based on policy
- Optional: allow user to select always-on VPN where device policy permits
- Steps: VPN > Add > Type: IKEv2 or IPSec, depending on server
- Enter server address, remote ID, and credentials
- Assign to groups and save
Windows 10/11
- VPN type: IKEv2 is common for Windows environments
- Authentication: certificate-based or username/password; also consider Azure AD for modern auth
- Server address: FQDN or IP
- Destination: remote access gateway details
- Provisioning: ensure the VPN connection name matches the profile for ease of use
- Add connection: you can rely on Intune to push the profile with all required details
- Assign profile to targeted devices or users, monitor deployment status
Deploy and assign the profile
- Scope tags optional and assignments: choose the groups that should receive the VPN profile
- Exclusions: create exclusion groups if certain devices should not get the profile
- End-user experience: provide clear instructions or a short video explaining how to connect to VPN after enrollment
- Save: validate the profile appears in the list of configurations
- Monitor deployment: check status under Devices > Configuration profiles > > View reports
Test and verify connectivity
- Pilot group: start with a small group of devices to catch issues early
- Validation steps:
- Enrollment complete on target device
- VPN profile appears in the device’s network settings
- User initiates a VPN connection and authenticates
- Verify access to internal resources e.g., intranet site, internal apps
- Confirm no unintended data leakage or traffic routing issues
- Common checks:
- Endpoint resolution server address accessible
- Certificate validity if using cert-based
- Split tunneling rules effective
- Auto-connect behavior and disconnect/reconnect reliability
Platform-specific steps condensed quick-start iOS quick-start
- Create VPN profile with IKEv2
- Use certificate-based authentication if possible
- Enable auto-connect if policy allows
- Deploy to iOS device groups
Android quick-start Cant uninstall nordvpn heres exactly how to get rid of it for good: Quick, Easy, and Safe Uninstall Guide
- Choose IKEv2/IPsec or L2TP/IPsec depending on server
- Deploy client cert if required
- Decide on split tunneling policy
- Target Android device groups
Windows quick-start
- Use IKEv2 with certificate-based or username/password
- Ensure server address and IDs are correct
- Push via Intune and verify on a Windows test device
Security and compliance considerations
- Certificate management: ensure PKI is robust and devices receive valid certs
- Authentication: prefer modern authentication methods where possible
- Least privilege: VPN access restricted to necessary internal resources
- Device health: ensure devices meet minimum OS version and security baselines before enrollment
- Audit logs: enable monitoring of VPN connection attempts and access events
- Credential hygiene: encourage MFA for VPN access if supported
Monitoring and auditing
- Use Intune reporting to track deployment status, success rates, and device compliance
- Cross-check VPN server logs for authentication failures
- Establish a monthly review cadence to assess certificate expirations and renewals
- Create dashboards showing:
- Number of devices with VPN profile deployed
- VPN connection success rate
- Average connection time
- Access success to critical internal resources
Common issues and troubleshooting
- Devices not receiving the VPN profile
- Check scope assignments and group membership
- Verify enrollment status on devices
- VPN connection fails at startup
- Validate server address, IDs, and certificate validity
- Confirm VPN service is reachable from the device network
- Authentication failures
- Ensure user accounts have proper permissions and MFA is configured
- Check certificate validity and chain trust
- Split tunneling not behaving as expected
- Review network routes on the device and VPN server policy
- Confirm firewall rules permit desired traffic
- Performance issues
- Check VPN server load and geographic proximity of endpoints
- Validate MTU settings and fragmentation handling
Best practices and tips The Best Free VPN for China in 2026 My Honest Take What Actually Works in 2026
- Use descriptive naming conventions for profiles and groups
- Test in a controlled pilot before full rollout
- Maintain separate profiles for different platforms to avoid cross-platform drift
- Keep VPN server endpoints documented and updated in Intune notes
- Schedule periodic certificate renewals and automate where possible
- Document user-facing steps in a quick-start guide or FAQ for IT support
Security checklist
- Ensure certificate trust is established on all devices
- Enforce MFA for VPN access
- Disable split tunneling if sensitive data could be exposed
- Regularly rotate VPN credentials and certificates
- Implement incident response playbooks for VPN-related breaches
FAQ Section Frequently Asked Questions
How do I start the VPN profile creation in Intune?
Begin in the Microsoft Endpoint Manager admin center, go to Devices > Configuration profiles, and create a new VPN profile for your target platform.
Which platforms are supported for VPN profiles in Intune?
Intune supports iOS/iPadOS, Android, and Windows 10/11 for VPN profiles. macOS support is available with configuration profiles too but may require separate steps.
What VPN types are commonly used with Intune?
IKEv2 is a popular choice due to broad support and strong security, but L2TP/IPsec and platform-specific VPN types are also used depending on your server capabilities. Vpn gratuita microsoft edge as melhores extensoes seguras e como instalar
Can I use certificate-based authentication?
Yes. Certificate-based authentication is a common and secure method, typically paired with a PKI and an Intune certificate profile.
How do I test a VPN profile after deployment?
Enroll a test device, verify the VPN profile appears, connect, and validate access to internal resources. Check for any errors in Intune deployment reports and VPN server logs.
How do I manage split tunneling?
Split tunneling can be configured per platform depending on your VPN server setup. In Intune, you can set network traffic rules within the VPN profile.
What should I do if a device doesn’t receive the VPN profile?
Double-check the device’s enrollment status, group membership, and profile assignments. Verify there aren’t conflicting profiles and that the device has internet access to pull the profile.
How can I monitor VPN deployments?
Use Intune’s configuration profile reports to track deployment status, and review VPN server logs for authentication attempts and connection events. Troubleshooting Sophos VPN Why It Won’t Connect and How to Fix It
What are best practices for naming VPN profiles?
Use concise, descriptive names like Corp-Remote-VPN-IKEv2-Prod or Corp-Remote-VPN-Android-L2TP to reduce confusion during troubleshooting.
Do I need to renew VPN certificates?
Yes, certificates have expiration dates. Set up a renewal policy and automate distribution to devices to avoid outages.
Useful URLs and Resources text only
- Microsoft Intune documentation - https://learn.microsoft.com/en-us/mem/intune/
- Windows VPN configuration in Intune - https://learn.microsoft.com/en-us/mem/intune/configuration/vpn-settings-windows
- iOS VPN configuration in Intune - https://learn.microsoft.com/en-us/mem/intune/configuration/vpn-settings-ios
- Android VPN configuration in Intune - https://learn.microsoft.com/en-us/mem/intune/configuration/vpn-settings-android
- Azure AD conditional access overview - https://learn.microsoft.com/en-us/azure/active-directory/conditional-access
- Certificate-based auth in Intune - https://learn.microsoft.com/en-us/mem/intune/security/certificates
- VPN best practices for enterprises - https://www.cisco.com/c/en/us/products/security/vpn-endpoint-security-essentials/white-paper-list.html example
- NordVPN corporate solutions overview - https://nordvpn.com/are-you-a-business/ affiliate link guidance varies by page
- VPN troubleshooting guide - https://www.tenable.com/blog/vpn-troubleshooting-guide
Appendix: quick reference cheat sheet
- Create VPN profile: Devices > Configuration profiles > Create profile > Platform > VPN > configure settings > assign
- Common server types: IKEv2, IPsec, L2TP
- Authentication methods: certificate-based, username/password, MFA-enabled
- Deployment targets: user groups, device groups
- Validation steps: enrollment, profile presence, connect, resource access
End of guide: you’ve got the essential steps and best practices to create a VPN profile in Microsoft Intune step by step guide 2026. Ready to secure your organization’s remote access with confidence? If you’re watching this as a video, I’ll walk you through live screens showing each of these steps so you can replicate without missing a beat. And if you want a simple, reliable VPN option for your devices, considerNordVPN for secure, easy coverage across teams—check the overview in the affiliate section above for quick access. Outsmarting the Unsafe Proxy or VPN Detected on Now GG: Your Complete Guide
Sources:
Surfshark vpn port forwarding the ultimate guide to getting it right
Nordvpn 優惠碼 2026:香港最齊全折扣攻略,享高達75 off 額外 增強版攻略與實測
Does nordvpn block youtube ads and how it actually works with YouTube ads, CyberSec, and additional blockers
Open vpn edge: the ultimate guide to setup, security, and performance for OpenVPN Edge 2026
免费节点 clash:完整指南與最新資源,節省成本又穩定的 VPN 導覽 Setting Up Intune Per App VPN With GlobalProtect for Secure Remote Access: Quick Guide, Tips, and Best Practices
Renata Uzunov has been writing about consumer technology since 2018, with bylines covering privacy law, Wireguard, and router firmware. Approaches each review by setting up the product the same way a typical reader would and recording every snag along the way.